Marco Alcala's Blog
Cybersecurity insights and practical guidance for IT professionals and organizations.
Friends and colleagues, I co-authored this new book on CMMC compliance with 20 other cybersecurity experts from around the world. In this book, we provide guidance to successfully get the...

More Stories
Verifying Wire Transfer Requests
Verifying the authenticity of a wire transfer request is an important step in preventing scams and avoiding losing money. Here is a procedure to follow: Verify the sender's identity: Before...

Keeping Local Backups Isolated from Production
There are several ways to keep a local backup copy isolated from the production network. Here are some suggestions: Use a physically separate network: One way to isolate the backup...

Removing Users from the Windows Local Administrators Group
Removing users from the local administrators group in Microsoft Windows can be done using the following steps: Log in to Windows with an account that has administrator privileges. Open the...

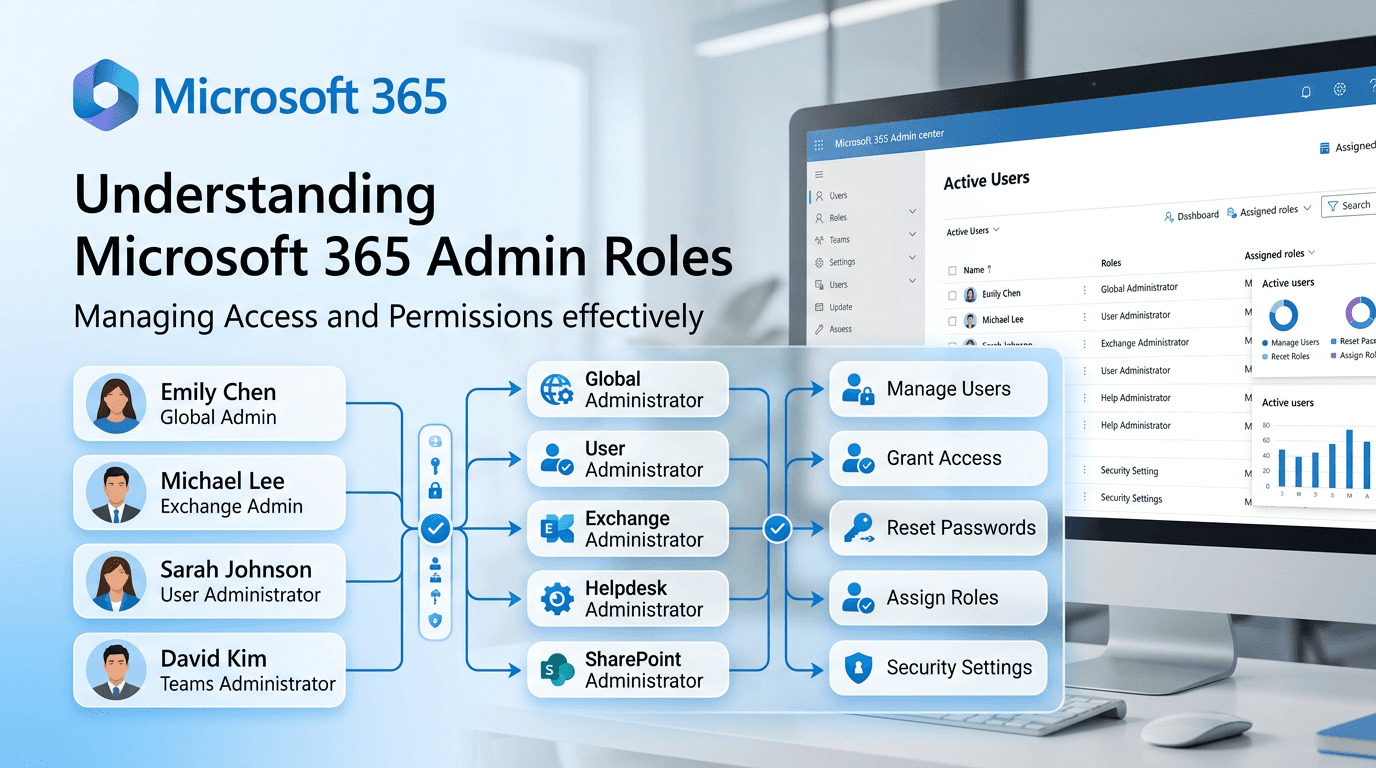
Revoking Admin Roles from Non-IT Users in Microsoft 365
To revoke admin roles from a non-IT user in Microsoft 365, you will need to follow these steps: Sign in to the Microsoft 365 Admin Center with your admin credentials....

Removing Admin Rights from a Mac User Account
As the owner or administrator of a Mac computer, you may need to remove admin rights from a user account for security purposes. Here are the steps you can follow...

Setting Up and Customizing Chromebooks
Chromebooks are designed to be simple and easy to use, but that doesn't mean you can't customize them to your needs. One way to do this is by setting up...

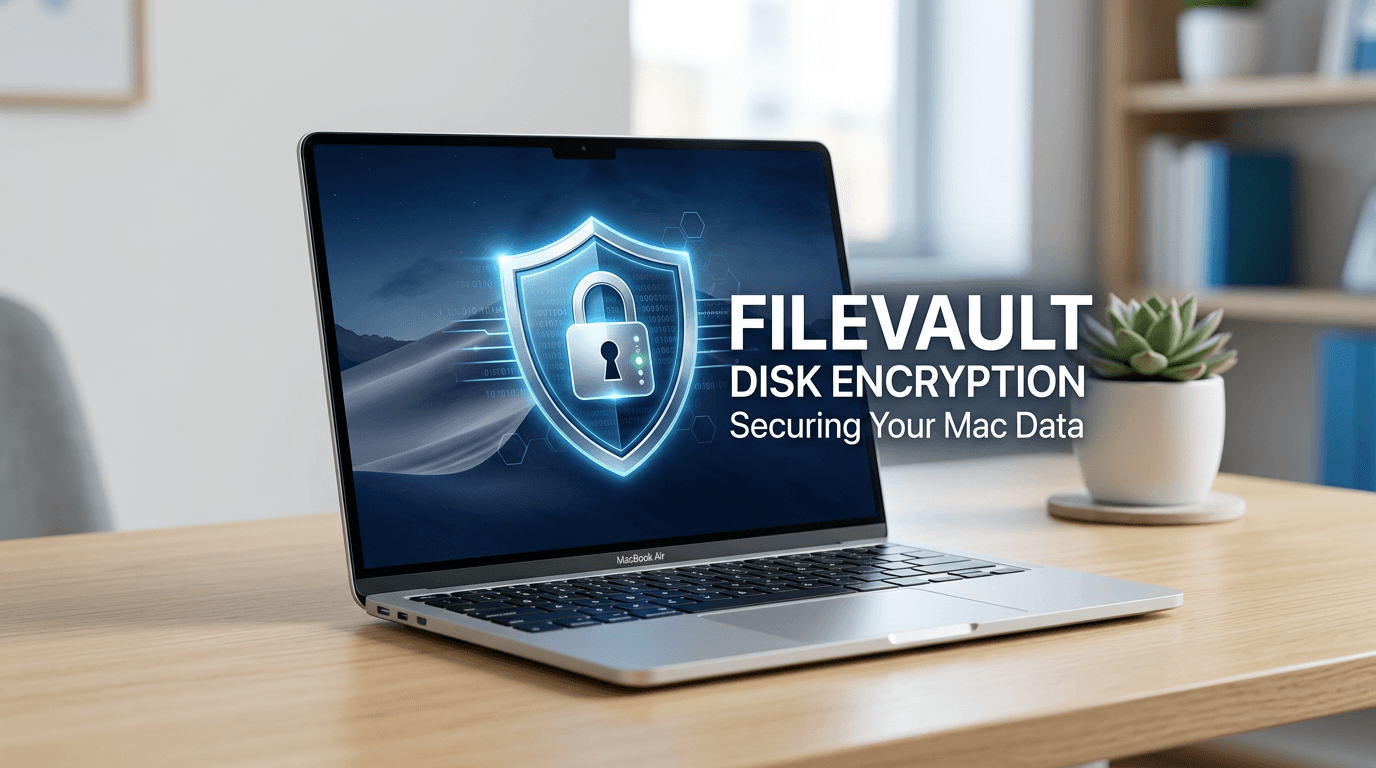
Understanding Apple FileVault Disk Encryption
Apple FileVault is a feature built into macOS that allows you to encrypt your hard drive to protect your data from unauthorized access. When enabled, FileVault uses XTS-AES 128-bit encryption...

Data Security Through Encryption
In today's digital age, data security is of utmost importance, and one of the best ways to secure data is through encryption. Encryption involves converting data into a code that...

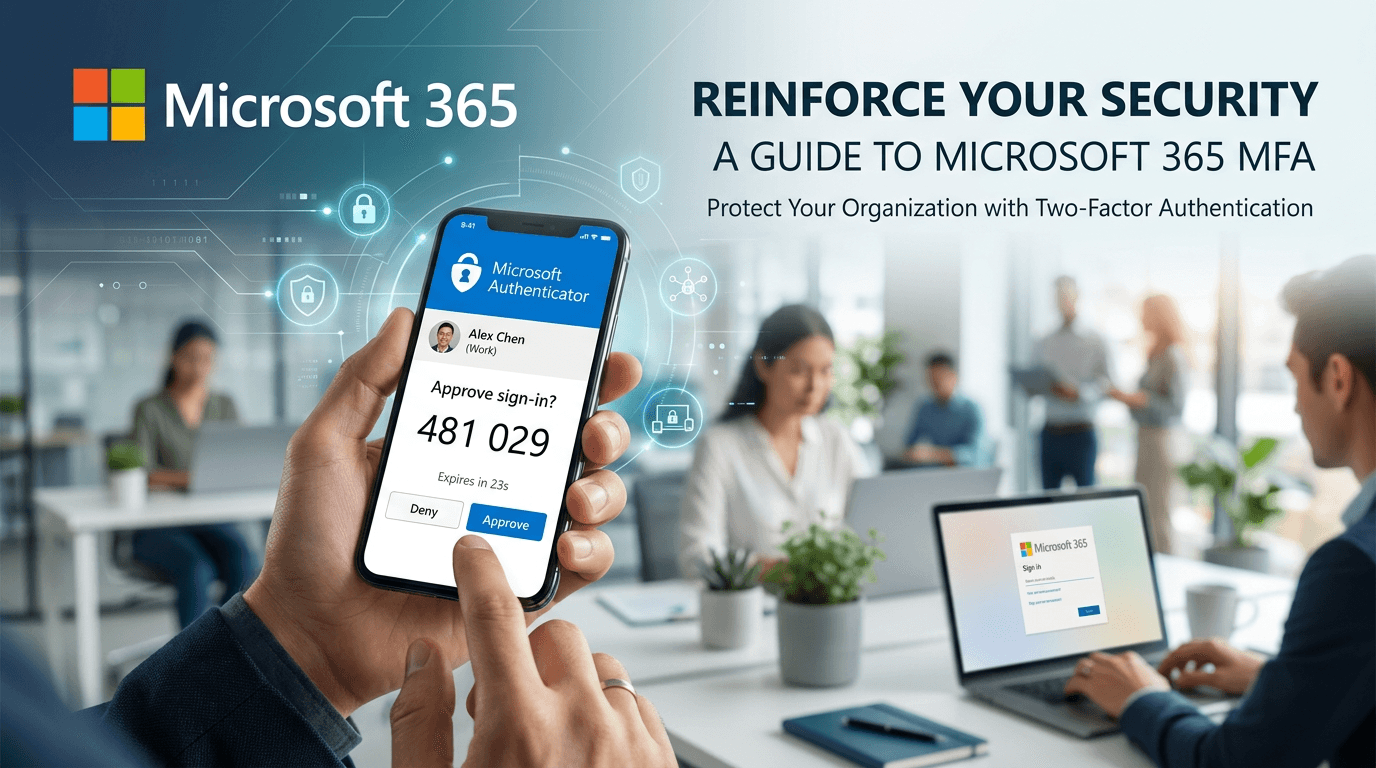
Implementing Multi-Factor Authentication for Microsoft 365
Multi-factor authentication (MFA) is a crucial security measure that provides an additional layer of protection to your Microsoft 365 account. By implementing MFA, you can prevent unauthorized access to your...